Domain whitelisting is a method of ensuring that no one but your organization is using your web picker. It’s one way of securing your solution and your resources, so others don’t attempt to piggy back on your account. At the same time, it isn’t entirely foolproof on its own; it requires other security measures. It’s a good idea to learn more about the technology behind your security to reduce your risk.
Here’s what you need to know about domain whitelisting and generally securing your application credentials, in terms of Filestack’s secure file upload service.
What is Domain Whitelisting?
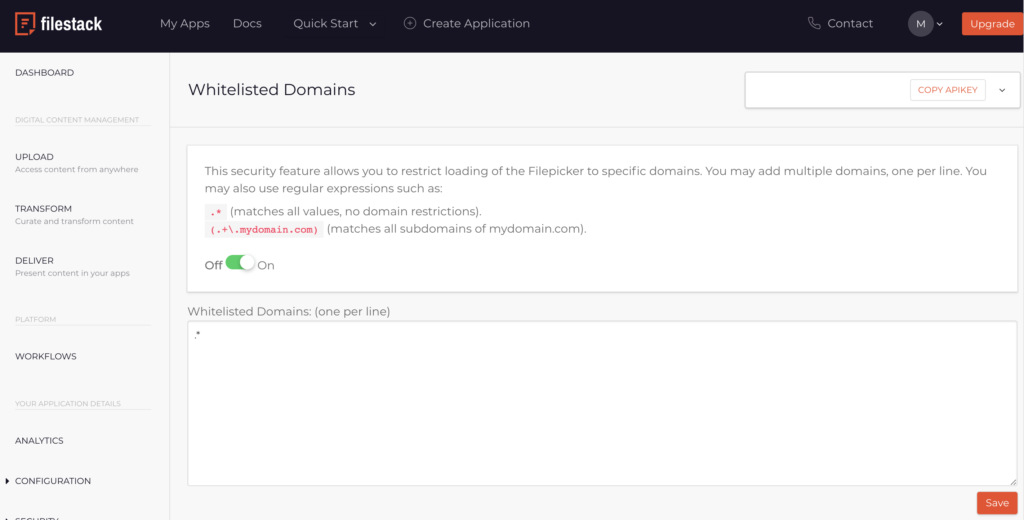
Within Filestack, domain whitelisting tells Filestack which domains it should expect to be placing requests. If a domain sends a request that isn’t one of the approved domains, then the web picker will not work. You will need to add any domains that you’re using to the domain whitelist manually. This domain will then be sent through the “Origin” header to the web picker.
This prevents any unauthorized use of the web picker within a browser, but it cannot stop an Origin header from being spoofed outside of a browser. Because of this, it can be used to prevent your resources from being used by another website, but it cannot protect against other types of attack. To protect against other types of attack, you will need to configure your authentication for every request.
API keys can be compromised through the front-end. Once an API key is distributed, it can be used by numerous other applications. This can drive up resource use quickly before it is caught. It can also present other security risks, if the API key is misused.
Why is Domain Whitelisting Important?
Whitelisting is less well-known than blacklisting. Under blacklisting, you specifically exclude sites that you don’t want to connect to something. Whitelisting instead specifically includes sites that you do want to allow to connect to something. Since whitelisting is more exclusive, it’s also far more secure. Of course, you need to list every domain that you use.
This can be completed through regular expressions, if there are a number of domains that need to be verified: “*.domain.com” as an example can be used to allow any subdomains on “domain.com”.
If your API key is included in the front end of your application, it can be viewed by users—but if you use domain whitelisting, having your API key exposed becomes a nonissue. Nevertheless, API keys can’t be removed entirely: API keys are necessary in order to tell the application what connections to expect. This is what makes it important to have multiple layers of security.
API keys are the primary method of securing a connection between applications, passing an authentication password from one application to the other. Compromised API keys have led to some tremendous security breaches, as it means that authentication and application content can be “hijacked.” It can even mean that data can be hijacked and compromised, under certain scenarios.
If you want to ensure that your domain whitelisting operates correctly, make sure that you include any subdomains and test domains that you’ll be using. IP addresses can also be whitelisted in the place of domains for additional security, or if you’re still in development and are connecting without a user-friendly domain.
Can Domain Whitelisting Protect from Everything?
Domain whitelisting is not a complete solution. It’s specifically intended to prevent your secure upload system from being used by an application that is originating from off your domain. This commonly happens when someone wants to utilize the same security and content management features that you are, but does not want to pay for file upload security.
However, any dedicated attack or hack is going to be able to bypass domain whitelisting. It’s not intended as a major security feature, but rather a way to reduce risk. Additional authentication solutions will be needed to secure app content and to make sure your secure upload system isn’t used by a malicious attacker, such as authenticating every request.
When managing your API, your primary concern is going to be securing the communications that move from your application to Filestack. If a connection is unencrypted or unsecured, it could potentially be vulnerable to malicious attackers or hijackers. Once files are already on the Filestack servers and being analyzed by Filestack, they will be secured by Filestack’s technology.
Domain whitelisting is only one of the tools that Filestack offers to secure your content management and secure upload solutions. Filestack provides advanced content transformation, workflow, and secure upload features. If you’re concerned about authentication and privacy services, you can communicate with Filestack’s team. To learn more, sign up for a free demo today.
Filestack is a dynamic team dedicated to revolutionizing file uploads and management for web and mobile applications. Our user-friendly API seamlessly integrates with major cloud services, offering developers a reliable and efficient file handling experience.
Read More →